IOSG: From "Fat Protocol" to "Fat Application", Interpreting the Appchain Narrative in 2025
By Jiawei @IOSG
Three years ago, we wrote an article about Appchain, which was triggered by dYdX’s announcement that it would migrate its decentralized derivatives protocol from StarkEx L2 to the Cosmos chain and launch its v4 version as an independent blockchain based on the Cosmos SDK and Tendermint consensus.
In 2022, Appchain may be a relatively marginal technology option. As we head into 2025, with the launch of more and more Appchains, particularly Unichain and HyperEVM, the market's competitive landscape is quietly shifting, and a trend centered around Appchain is forming. This article will explore our Appchain Thesis from this perspective.
Uniswap and Hyperliquid
▲ Source: Unichain
The idea of Unichain emerged quite early. Nascent founder Dan Elitzer published "The Inevitability of UNIchain" in 2022, highlighting Uniswap's scale, brand, liquidity structure, and demand for performance and value capture, pointing to the inevitability of its launch. Discussions about Unichain have been ongoing ever since.
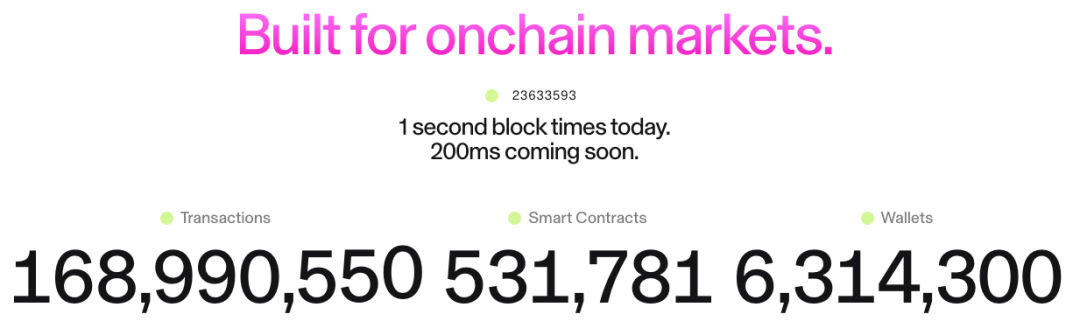
Unichain officially launched in February, and over 100 applications and infrastructure providers have already built on it. Its current TVL is approximately $1 billion, ranking it among the top five L2 platforms. Flashblocks with a 200ms block time and the Unichain Verification Network will be launched in the future.

▲ Source: DeFiLlama
As a perp, Hyperliquid has clearly had a need for Appchain and deep customization since day 1. In addition to its core products, Hyperliquid also launched HyperEVM, which, like HyperCore, is protected by the HyperBFT consensus mechanism.
In other words, in addition to its own powerful perp products, Hyperliquid is also exploring the possibility of building an ecosystem. Currently, the HyperEVM ecosystem has exceeded $2 billion in TVL, and ecological projects are beginning to emerge.
From the development of Unichain and HyperEVM, we can intuitively see two points:
- The L1/L2 competitive landscape is beginning to diverge. The combined TVL of the Unichain and HyperEVM ecosystems exceeds $3 billion. These assets would have previously been concentrated on general-purpose L1/L2 platforms like Ethereum and Arbitrum. The independent development of top applications has directly led to a loss of these platforms' core value sources, including TVL, transaction volume, transaction fees, and MEV.
In the past, L1/L2 and applications like Uniswap and Hyperliquid enjoyed a symbiotic relationship: applications brought activity and users to the platform, while the platform provided security and infrastructure for the applications. Now, Unichain and HyperEVM have become platform layers themselves, forming a direct competitive relationship with other L1/L2 chains. They are not only competing for users and liquidity, but also for developers, inviting other projects to build on their chains. This has significantly changed the competitive landscape.
- Unichain and HyperEVM's expansion paths are distinct from existing L1/L2 models. While the latter often build infrastructure first and then attract developers with incentives, Unichain and HyperEVM's model is product-first—they first establish a market-proven core product with a large user base and brand recognition, and then build an ecosystem and network effects around this product.
This approach is more efficient and sustainable. Instead of "buying" the ecosystem through high developer incentives, they "attract" it through the network effects and technological advantages of their core products. Developers choose to build on HyperEVM because of the high-frequency trading users and real demand scenarios there, not because of vague incentive promises. This is clearly a more organic and sustainable growth model.
What has changed in the past three years?
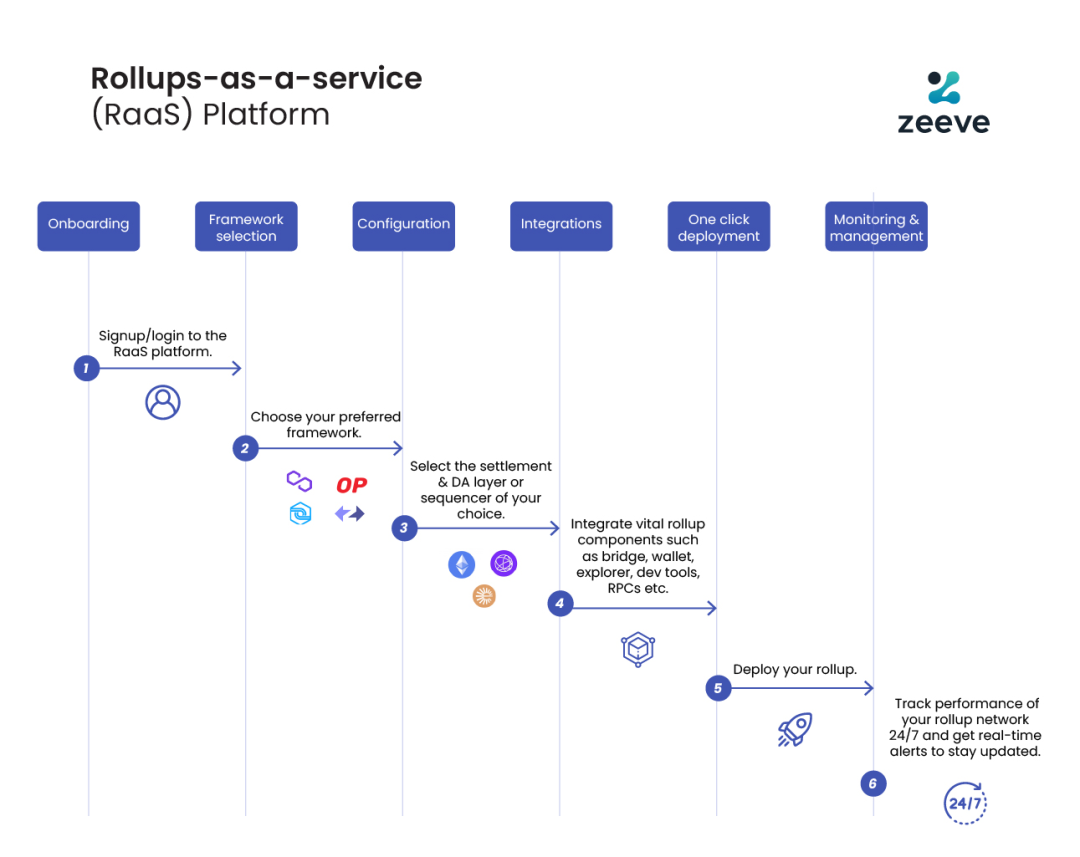
▲ Source: zeeve
First, the maturity of the technology stack and the development of third-party service providers. Three years ago, building an Appchain required teams to master the full blockchain stack. However, with the development and maturity of RaaS services like OP Stack, Arbitrum Orbit, and AltLayer, developers can now combine modules on demand, from execution and data availability to settlement and interoperability, much like using cloud services. This significantly reduces the engineering complexity and initial capital investment required to build an Appchain. The shift in operating models from self-built infrastructure to purchased services provides flexibility and feasibility for innovation at the application layer.
Secondly, brand and user mindset are key factors. We all know that attention is a scarce resource. Users are often loyal to an application's brand, not its underlying technology: they use Uniswap for its user experience, not because it runs on Ethereum. With the widespread adoption of multi-chain wallets and further improvements in UX, users will become almost unaware of using different chains—their first points of contact are often wallets and applications. When applications build their own chains, users' assets, identities, and usage habits are embedded within the application ecosystem, creating a powerful network effect.
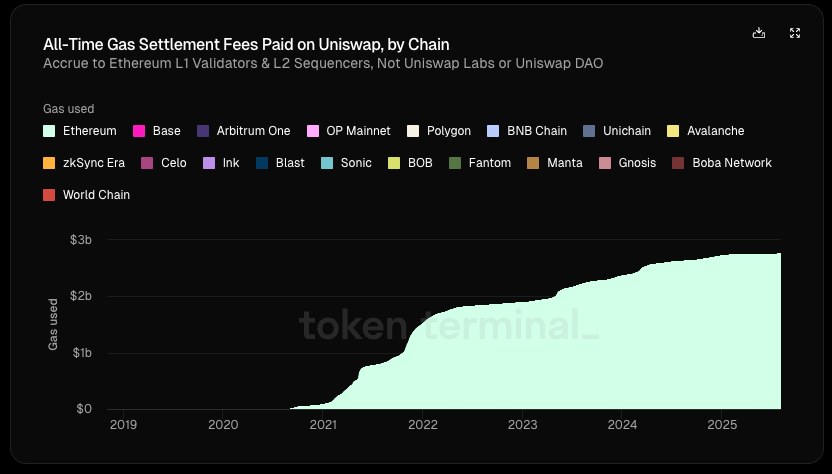
▲ Source: Token Terminal
Most importantly, applications are increasingly pursuing economic sovereignty. In traditional L1/L2 architectures, we can see a clear "top-down" trend in value flows:
- Application layer creates value (Uniswap trading, Aave lending)
- Users pay fees for using the application (application fees + gas fee), part of these fees go to the protocol, and part goes to LPs or other participants
- 100% of the gas fees go to L1 validators or L2 sorters
- MEV is divided among searchers, builders and validators in different proportions
- Ultimately, L1 tokens capture other values besides app fees through staking
In this chain, the application layer that creates the most value actually captures the least.
According to Token Terminal, of Uniswap's $6.4 billion in total value creation (including LP returns, gas fees, etc.), the protocol/developers, equity investors, and token holders have received less than 1%. Since its launch, Uniswap has generated $2.7 billion in gas revenue for Ethereum, which is roughly 20% of Ethereum's settlement fees.
But what if the application has its own chain?
They can collect gas fees for themselves and use their own tokens as gas tokens; internalize MEV, minimize malicious MEV by controlling the sorter, and return benign MEV to users; or customize the fee model to achieve a more complex fee structure, etc.
In this light, seeking to internalize value becomes the ideal choice for applications. When an application's bargaining power is sufficiently strong, it will naturally demand greater economic benefits. Therefore, high-quality applications have a weak dependency on the underlying chain, while the underlying chain has a strong dependency on high-quality applications.
summary
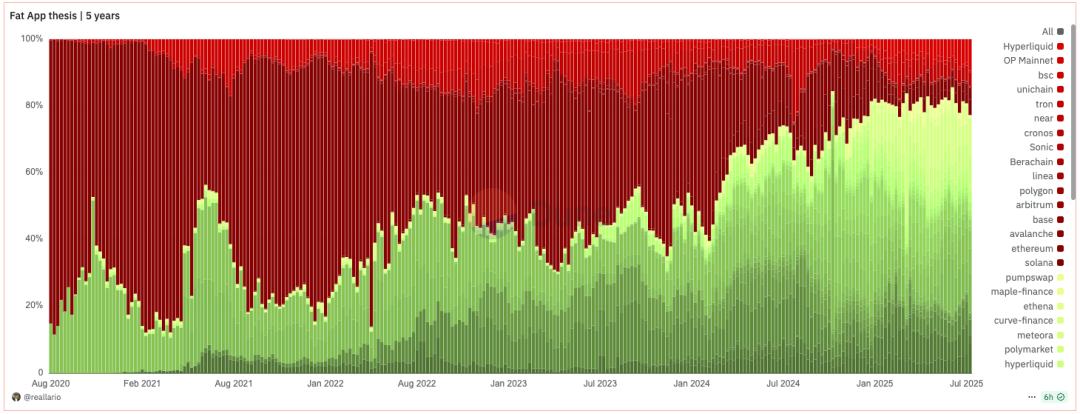
▲ Source: Dune@reallario
- The chart above roughly compares the revenue of protocols (red) and applications (green) since 2020. We can clearly see that the value captured by applications has been gradually increasing, reaching approximately 80% this year. This may, to some extent, overturn Joel Monegro's famous theory of "fat protocols, thin applications."
We are witnessing a paradigm shift from the "fat protocol" theory to the "fat application" theory. Historically, the pricing logic for crypto projects has primarily focused on technological breakthroughs and the development of underlying infrastructure. In the future, pricing will gradually shift to a more focused approach based on brand, traffic, and value capture. If applications can easily build their own chains based on modular services, L1's traditional "rental collection" model will be challenged. Just as the rise of SaaS has reduced the bargaining power of traditional software giants, the maturity of modular infrastructure is also weakening L1's monopoly.
In the future, the market capitalization of leading applications will undoubtedly exceed that of most L1s. The valuation logic for L1s will shift from "capturing the total value of the ecosystem" to a stable, secure, decentralized "infrastructure service provider." Its valuation will be closer to that of public goods generating stable cash flows, rather than "monopolistic" giants that capture the majority of the ecosystem's value. Its valuation bubble will be squeezed to a certain extent. L1s will also need to rethink their positioning.
- Our view on Appchain is that, thanks to its brand, user awareness, and highly customized on-chain capabilities, Appchain can better capture long-term user value. In the era of "fat apps," these applications not only capture the direct value they create but also build blockchains around them, further externalizing the value and capturing the value of the infrastructure. They are both products and platforms, serving both end users and other developers. In addition to economic sovereignty, top applications will also seek other sovereign rights: the right to decide on protocol upgrades, transaction ordering and censorship resistance, and ownership of user data.
- Of course, this article primarily explores Appchain in the context of top applications like Uniswap and Hyperliquid, which have already launched Appchain. Appchain's development is still in its early stages (Uniswap still holds 71.4% of the total value (TVL) on Ethereum). Protocols like Aave, which involve wrapped assets and collateral and rely heavily on composability on a single chain, are also less suitable for Appchain. Relatively speaking, per-platforms whose only external requirements are oracles are more suitable for Appchain. Furthermore, Appchain isn't the best choice for mid-tier applications, requiring a case-by-case analysis. I won't elaborate further here.
You May Also Like

The Role of Blockchain in Building Safer Web3 Gaming Ecosystems
- Immutable Ownership of Assets Blockchain records can be manipulated by anyone. If a player owns a sword, skin, or plot of land as an NFT, it is verifiably in their ownership, and it cannot be altered or deleted by the developer or even hacked. This has created a proven track record of ownership, providing control back to the players, unlike any centralised gaming platform where assets can be revoked.
- Decentralized Infrastructure Blockchain networks also have a distributed architecture where game data is stored in a worldwide network of nodes, making them much less susceptible to centralised points of failure and attacks. This decentralised approach makes it exponentially more difficult to hijack systems or even shut off the game’s economy.
- Secure Transactions with Cryptography Whether a player buys an NFT or trades their in-game tokens for other items or tokens, the transactions are enforced by cryptographic algorithms, ensuring secure, verifiable, and irreversible transactions and eliminating the risks of double-spending or fraudulent trades.
- Smart Contract Automation Smart contracts automate the enforcement of game rules and players’ economic exchanges for the developer, eliminating the need for intermediaries or middlemen, and trust for the developer. For example, if a player completes a quest that promises a reward, the smart contract will execute and distribute what was promised.
- Anti-Cheating and Fair Gameplay The naturally transparent nature of blockchain makes it extremely simple for anyone to examine a specific instance of gameplay and verify the economic outcomes from that play. Furthermore, multi-player games that enforce smart contracts on things like loot sharing or win sharing can automate and measure trustlessness and avoid cheating, manipulations, and fraud by developers.
- Cross-Platform Security Many Web3 games feature asset interoperability across platforms. This interoperability is made viable by blockchain, which guarantees ownership is maintained whenever assets transition from one game or marketplace to another, thereby offering protection to players who rely on transfers for security against fraud. Key Security Dangers in Web3 Gaming Although blockchain provides sound first principles of security, the Web3 gaming ecosystem is susceptible to threats. Some of the most serious threats include:

Vitalik Buterin Challenges Ethereum’s Layer 2 Paradigm
