After 16 billion data breaches: The ultimate security self-check manual that every encryption user should keep
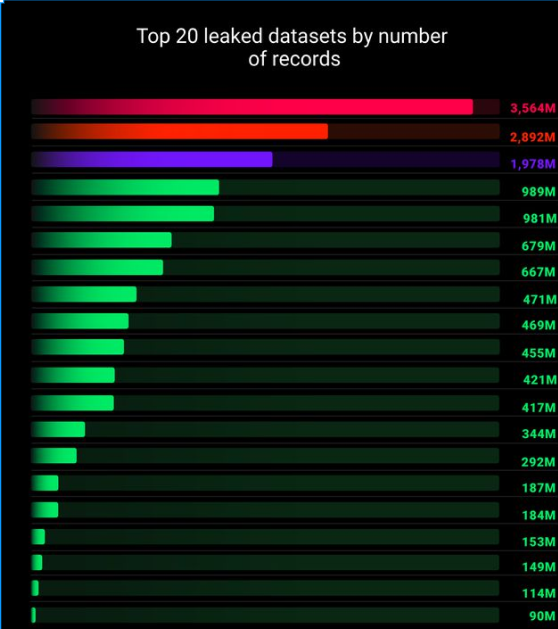
Recently, a data leak that is said to be the "largest in history" has been confirmed by multiple cybersecurity researchers. A huge database containing up to 16 billion login credentials is circulating on the dark web, and its source affects almost all mainstream platforms we use daily, such as Apple, Google, Facebook, and GitHub.
This is no longer a regular data leak, but a blueprint for a global hacker attack that can be "weaponized on a large scale". For everyone in the digital age, especially those who hold crypto assets, this is tantamount to an imminent security storm. This article will provide you with an ultimate security self-check manual. Please check it immediately and strengthen your asset defense line.
1. The threat is not limited to passwords: The "fatal" aspect of this leak
To understand the importance of defense, we must first understand the severity of the threat. The reason why this leak is fatal is that it contains far more sensitive information than ever before:
"Credential Stuffing" Attacks : Attackers are using leaked "email + password" combinations to automatically log into major cryptocurrency exchanges on a large scale. If you use the same or similar passwords on different platforms, your exchange account is likely to be hacked without you noticing.
The mailbox is stolen as a "master key" : Once the attacker controls your primary mailbox (such as Gmail) through the leaked password, they can use the "forgot password" function to reset all your associated financial and social accounts, making your SMS or email verification useless.
The "Achilles' heel" of the password manager : If the main password of the password manager you use is not strong enough, or 2FA is not enabled, then once the attacker cracks it, all the website passwords, mnemonics, private keys, and API keys that you think are safely stored in it will be "wiped out in one go."
Precise "social engineering" phishing : Scammers can use your leaked personal information (name, email address, frequently used websites, etc.) to disguise themselves as exchange customer service, DAO administrators, or even your familiar friends to conduct highly customized and hard-to-defend against precise phishing scams against you.
II. Action Manual: A three-dimensional defense system from accounts to chains
In the face of industrial-level security threats, we need to establish a three-dimensional defense system.
1. Account-level defense: Strengthen your digital door
Password Management
This is the most basic and urgent step. Please immediately change all key accounts (especially exchanges and emails) to a new, independent, complex password consisting of uppercase and lowercase letters + numbers + symbols .
2FA Upgrade
Two-factor authentication (2FA) is the "second lock" of your account, but its security is graded. Please immediately deactivate and replace SMS 2FA verification on all platforms! It is extremely vulnerable to SIM card swap attacks. Please switch to more secure authenticator apps such as Google Authenticator . For accounts holding large assets, you can use hardware security keys , which is currently the safest consumer-level protection method.
2. On-chain defense: cleaning up the invisible “backdoor” of wallets
Wallet security is not only about private keys. Your interaction with decentralized applications (DApps) may also leave risks. Please use professional tools such as DeBank and Revoke.cash immediately to comprehensively check which DApps your wallet address has authorized unlimited tokens (Approve) . For all applications that are no longer used, untrusted, or have too high authorization limits, immediately cancel their token transfer permissions and close the "backdoor" that may be exploited by hackers to prevent assets from being stolen without your knowledge.
3. Mental defense: Establishing a “zero trust” security concept
In addition to technical defense, mentality and habits are the last line of defense.
Establish the "zero trust" principle : In the current severe security environment, please maintain the highest level of vigilance for all requests for signatures, private keys, authorizations, wallet connections, and any links actively sent through emails, private messages, etc. - even if it comes from friends you trust (because their accounts may have been stolen).
Develop the habit of visiting official channels : Always visit the exchange or wallet website through your saved bookmarks or manually enter the official website address. This is the most effective way to prevent phishing websites.
Security is not a one-time operation, but a discipline and habit that needs to be maintained for a long time. In a digital world full of dangers, prudence is the only and ultimate way to protect our wealth.
You May Also Like

The Role of Blockchain in Building Safer Web3 Gaming Ecosystems
- Immutable Ownership of Assets Blockchain records can be manipulated by anyone. If a player owns a sword, skin, or plot of land as an NFT, it is verifiably in their ownership, and it cannot be altered or deleted by the developer or even hacked. This has created a proven track record of ownership, providing control back to the players, unlike any centralised gaming platform where assets can be revoked.
- Decentralized Infrastructure Blockchain networks also have a distributed architecture where game data is stored in a worldwide network of nodes, making them much less susceptible to centralised points of failure and attacks. This decentralised approach makes it exponentially more difficult to hijack systems or even shut off the game’s economy.
- Secure Transactions with Cryptography Whether a player buys an NFT or trades their in-game tokens for other items or tokens, the transactions are enforced by cryptographic algorithms, ensuring secure, verifiable, and irreversible transactions and eliminating the risks of double-spending or fraudulent trades.
- Smart Contract Automation Smart contracts automate the enforcement of game rules and players’ economic exchanges for the developer, eliminating the need for intermediaries or middlemen, and trust for the developer. For example, if a player completes a quest that promises a reward, the smart contract will execute and distribute what was promised.
- Anti-Cheating and Fair Gameplay The naturally transparent nature of blockchain makes it extremely simple for anyone to examine a specific instance of gameplay and verify the economic outcomes from that play. Furthermore, multi-player games that enforce smart contracts on things like loot sharing or win sharing can automate and measure trustlessness and avoid cheating, manipulations, and fraud by developers.
- Cross-Platform Security Many Web3 games feature asset interoperability across platforms. This interoperability is made viable by blockchain, which guarantees ownership is maintained whenever assets transition from one game or marketplace to another, thereby offering protection to players who rely on transfers for security against fraud. Key Security Dangers in Web3 Gaming Although blockchain provides sound first principles of security, the Web3 gaming ecosystem is susceptible to threats. Some of the most serious threats include:

Vitalik Buterin Challenges Ethereum’s Layer 2 Paradigm
